TryHackMe - Inclusion Room
Another box down. It's NanoWrimo at the moment, so I'm not as efficient, but this box was super easy, and a great introduction to another tool, so let's do a writeup. This was TryHackMe's Inclusion Room
Reconnaissance
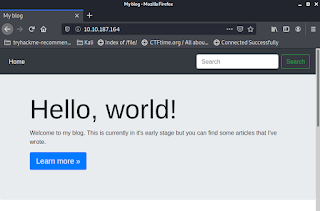
Let's see if the box has a website.
Neat. Is this a standard website?
Hmm. Looks custom. That might be a username too. Let's hang onto it for reference. Just to be sure, let's see what kind of server it is.
Python server. Neat. This blog must actually work. Check out the neat theming they did in the text of the articles.
Let's click on that LFI-Attack article and see how the site specifies which article we're viewing.
OK, neat. It uses the query string to specify the article. That should be easy to mess with. We know that this is an LFI challenge, so we might have enough info to skip to exploitation, but we should do our due dilligence.
Enumeration
Well, nothing but http and ssh on standard ports in nmap. Let's try gobuster.
Well, that was a bust (ba dum tsh). Let's see if we can attack that querystring after all.
Exploitation
Well, the article we're reading on the page about LFI Attacks, even mentions trying to get /etc/passwd so let's try that.
No dice. That said, an internal server error is a good sign. It means this query string probably isn't protected. Let's bust out BurpSuite. For those of you who haven't used it before, here's a brief breakdown of setup. Once you start it, clicking past all the dialogs, you should notice that it has a built-in proxy that is on by default.
This is on port 8080 normally, but you can check it right there on the Dashboard. Kali uses Firefox by default, so we'll want to snag FoxyProxy. Once that's installed, we just need to configure a new proxy for BurpSuite.
And then turn it on.
Then we can just refresh the LFIAttack article from the blog and Burp will intercept it.
I had to go to the Proxy tab manually, but that's easy because it's highlighted when it captures a request. We want to select Action and send this to the Intruder section of BurpSuite. This is important because we want to test different payloads.
By default, my payload was already set for the querystring: lfiattack. If yours isn't, you can just highlight it and select "add parameter". Then we'll head on over to the Payloads subtab so we can import a payload.
I'm lazy, so we're not going to enter a payload manually. We're going to go ahead and load it. I found a nice wordlist on Kali in /usr/share/wordlists/wfuzz/Injections called Traversal.txt. That sounds like exactly what we're looking for to do LFI. It should traverse around and see what directories we can find. So that's what I picked.
Then we just run the attack. And it didn't take long either. I sort my attack results by length, and just a few seconds in, we got a traversal to /etc/passwd. Nice!
We can scroll down to the bottom and see that our falcon user left his password in here.
Well, let's see if this is enough to SSH into the box.
It sure is! Is that user flag here?
It sure is! Nailed it!
Privilege Escalation
Let's see if we have any sudo permissions.
Socat eh? Let's check GTFOBins, and sure enough: https://gtfobins.github.io/gtfobins/socat/#sudo
That seems like a simple enough script. Let's run it.
Nice. My shell sucks, but meh, let's see if we can find the root flag.
And that concludes another box! Let's keep 'em comin'!






















Comments
Post a Comment