TryHackMe - Simple CTF Room
Wow! Just wow! I finished my first CTF yesterday, and before you know it, I have finished another one! Let's do a writeup on the Simple CTF room.
Reconnaissance
Let's check the IP and see if there's a website there
Sweet. Looks like we have an Apache 2 Server running on Ubuntu. I think I can find the version number on this page, but I'm going to be lazy and check the error message for the version number.
Sweet, we know it's version 2.4.18. Well' that's all we can do without starting to enumerate. Let's move on.
Enumeration
We start with nmap as per usual.
Well, that answers the first 2 questions in the room. ssh is running on the port above 1000, and there's 2 services running below port 1000. SSH is running on 2222 instead of the standard port 22. We should remember that in case we get the opportunity to ssh into the box later.
Well, ftp is open. Port 21 is ftp, not SFTP (usually runs on the same port as ssh). So that may be an insecure version. Let's run the nmap script to log into the FTP server anonymously just to check if we can do that.
Darn. No luck there. Meh, no worries. Let's keep looking. Since we know there's an apache HTTP server, let's run gobuster and check for subdirectories. Maybe there's something here after all.
I'll be honest, I spent time searching through robots.txt and server-status, but those are standard pages. The page I should've looked at first was /simple.
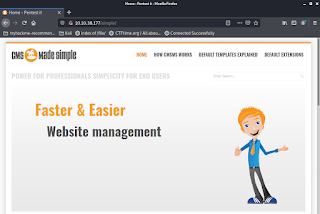
Cool, a default website. Let's scroll down and check the version number.
Awesome. CMS Made Simple 2.2.8 Let's plug that into a google search along with CVE to look for vulnerabilities.
Jackpot https://www.exploit-db.com/exploits/46635. Before we dig in, let's take a look at what else this CMS has to offer with another round of gobuster. This might pay off later, who knows.
I'll tell you I went down this rabbit hole a bit. These are definitely other potential vulnerabilites, but we had a bird in the hand which is worth more than two in the bush.
If we go back to the room, we actually find that CVE-2019-9053 (the one we found earlier) is the answer to the next question. It is a sqli (sql injection) vulnerability, which is the answer to the question after that. Well, we found a vulnerability. We could enumerate further, but let's move on since the room clearly is intended for us to go this route.
Exploitation
I pulled down the script from the vulnerability page and dropped it into a text file and saved it as cve-2019-9053.py. I don't know if there's a better way that the professionals do it, but that's what I did. I tried to run it and ran into some issues. Turns out it has some python dependencies. Kali doesn't even come with pip installed, so I had to install it, then the dependencies.
"What a dumb dependency", I thought as I tried to run the code....crap. It is erroring on print statements that don't have parenthesis around them. This is python2 code. I just did all this for python3, and I can't even find a package for python2-pip since python2 is (as of late 2020) completely obsolete and no longer to be used. Fine, let's upgrade the script to python3.
I ran pip install 2to3, which I found with a quick google. Then I ran it manually from my ./local/bin directory which apparently isn't on PATH on kali. All of this was pretty obvious from the messages in the terminal but I don't have screenshots, sorry. So it ran fine:
Well, not so much. OK, script runs but has issues. I went through the code where there's a couple of notes. There's a comment that you need to tweak the "TIME" variable, so I changed it from 1 to 2 (and later to 3).
Well, that's better, but it still doesn't like this "encoded before hashing" stuff. I came across the answer on stackoverflow.
(str(salt) + word).encode('utf-8')
I tweaked the sline in the script where it tried to hash our passwords from our wordlist and ran it again.
and...
YAY!!! We did it! We found a login for the website. That's the answer to the next question about the password. Well, people reuse passwords all the time. Let's see if we can use it to ssh into the box.
We sure can! That also answers the next question. We can use that password to ssh. Well, let's see if we can find that user flag.
Easy Peasy. We have finished the exploitation phase! There's a followup question that we can check while we're still this user. Let's do that.
Privilege Escalation
So I did a cursory SUID scan just like the one that had worked on the previous box. No dice. Let's break out the big guns. I want LinPEAS. Sadly, the TryHackMe boxes don't have access to the outside world. So I knew I'd have to download it locally and host it on a temporary server so I could download it on the box. Thankfully this was all explained in the LinPEAS README file.
Cool, now to download it on the server. I struggled a bit because CURL didn't exist. So I spun up a real bash shell, which was a nice improvement, but still no CURL. Thankfully wget was still there.
Cool, now to run the script and see what we get. The output is ginormous, and I stopped the script after I found a useful vulnerability, so I'm not going to try to screenshot the whole thing. But this was the highlight:
VIM is a text editor. We shouldn't need root privileges to run a text editor. I'll be honest. I felt really dumb here. I should have just done this:
Checking what sudo privileges you have is usually a good cursory step before you bring in the big guns, but I was excited because how often do you get to run LinPEAS? Anyway, that's the answer to our next question. I just headed on over to GTFOBins: https://gtfobins.github.io/gtfobins/vim/#sudo was a quick find.
The first script worked perfectly.
Well, I think I pressed an arrow key or something, but still, pretty good. I rooted the box! Now to find that root flag!
Yeehaw! That's 2 boxes in 2 days! I'm having an awesome week!


















Off, this one gave me a run for my money. I found the CMS vulnurabilty, had to fiddle around with john, hashcat and finally a python script to get to the password. Then I went down the wrong path completely, and accessed a reverse shell on the machine, but that leads you to nowhere. User www-data seems to be a dead end.
ReplyDeleteSince I couldn't figure out a few of the answers even though I already was logged in I gave up and looked at a walkthrough. No wonder my ssh attempt didn't work... I did not specify the port! Once I was done facepalming the rest was pretty easy. But I learned that you can start a bash via vim!